PROTECTING FAMILIES • AI-POWERED DEFENSE • AUTOMATIC PROTECTION • ALWAYS ADAPTING • ZERO TECHNICAL KNOWLEDGE NEEDED • WORKS WHILE YOU SLEEP • FUTURE PROOF TECHNOLOGY • PROTECTING FAMILIES • AI-POWERED DEFENSE • AUTOMATIC PROTECTION • ALWAYS ADAPTING • ZERO TECHNICAL KNOWLEDGE NEEDED • WORKS WHILE YOU SLEEP • MILITARY TECHNOLOGY FOR FAMILIES • PROTECTING FAMILIES • AI-POWERED DEFENSE • AUTOMATIC PROTECTION • ALWAYS ADAPTING • ZERO TECHNICAL KNOWLEDGE NEEDED • WORKS WHILE YOU SLEEP • FUTURE PROOF TECHNOLOGY • PROTECTING FAMILIES • AI-POWERED DEFENSE • AUTOMATIC PROTECTION • ALWAYS ADAPTING • ZERO TECHNICAL KNOWLEDGE NEEDED • WORKS WHILE YOU SLEEP • FUTURE PROOF TECHNOLOGY •
PROTECTING FAMILIES • AI-POWERED DEFENSE • AUTOMATIC PROTECTION • ALWAYS ADAPTING • ZERO TECHNICAL KNOWLEDGE NEEDED • WORKS WHILE YOU SLEEP • MILITARY TECHNOLOGY FOR FAMILIES •
PROTECTING FAMILIES • AI-POWERED DEFENSE • AUTOMATIC PROTECTION • ALWAYS ADAPTING • ZERO TECHNICAL KNOWLEDGE NEEDED • WORKS WHILE YOU SLEEP • FUTURE PROOF TECHNOLOGY • PROTECTING FAMILIES • AI-POWERED DEFENSE • AUTOMATIC PROTECTION • ALWAYS ADAPTING • ZERO TECHNICAL KNOWLEDGE NEEDED • WORKS WHILE YOU SLEEP • MILITARY TECHNOLOGY FOR FAMILIES • PROTECTING FAMILIES • AI-POWERED DEFENSE • AUTOMATIC PROTECTION • ALWAYS ADAPTING • ZERO TECHNICAL KNOWLEDGE NEEDED • WORKS WHILE YOU SLEEP • FUTURE PROOF TECHNOLOGY • PROTECTING FAMILIES • AI-POWERED DEFENSE • AUTOMATIC PROTECTION • ALWAYS ADAPTING • ZERO TECHNICAL KNOWLEDGE NEEDED • WORKS WHILE YOU SLEEP • FUTURE PROOF TECHNOLOGY •
AUTOMATED THREAT REPORTING • FBI NOTIFICATION • ISP ALERTS • PARENTAL CONTROLS • ACTIVITY MONITORING • PREDATOR DETECTION • SCAM PREVENTION • RANSOMWARE BLOCKING • IDENTITY PROTECTION • SMART HOME DEFENSE

Hackers use AI to create new attacks faster than traditional security can keep up. They adapt, they learn, and they never sleep. Your family needs protection that's just as smart and just as relentless.
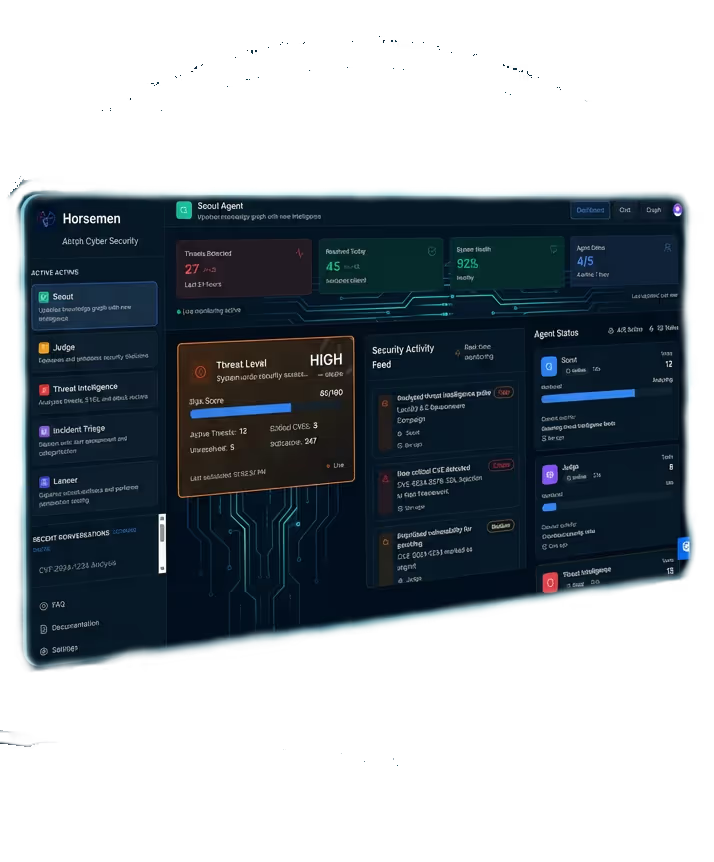
Horsemen uses the same AI technology that protects military systems—redesigned to protect families automatically, with zero technical expertise required.





Meanwhile, scammers mimic bank emails to steal passwords and hackers break into smart home devices. Today's threats are faster, smarter, and anyone can launch them with minimal resources.
Traditional antivirus software only reacts after damage is done. Sleight works differently—it catches threats before they reach your family.

.avif)











Deception-based cyber self-defense for individuals and families.

